2048 Bit Rsa Key Generator
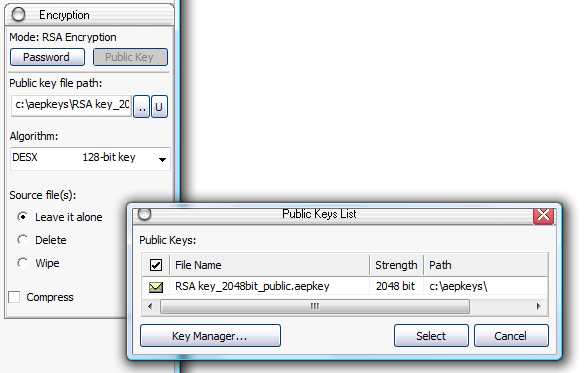
Mar 03, 2020 Cloud IoT Core supports the RSA and Elliptic Curve algorithms. For details on key formats, see Public key format. Generating an RSA key. You can generate a 2048-bit RSA key pair with the following commands: openssl genpkey -algorithm RSA -out rsaprivate.pem -pkeyopt rsakeygenbits:2048 openssl rsa -in rsaprivate.pem -pubout -out rsapublic.pem. Online RSA key generation: RSA (Rivest, Shamir and Adleman) is an asymmetric (or public-key) cryptosystem which is often used in combination with a symmetric cryptosystem such as AES (Advanced Encryption Standard).
18 June 2013- RSA key 2048 bit MY router is 1024 bits. If you run the command on your router it should be 2048. 0 Helpful Reply. Latest Contents. AnyConnect Syslog Configuration Example. Created by pcarco on 10:54 AM.
- Nov 07, 2001 The X509v3 Certificate Generator (XCG) enables users to parse and decode X509v3 certificates and to generate self-signed X509v3 certificates. However the application DOES NOT implement all options of the X509v3 (actually v7) standard. Certificates can contain 2048 or 4096 bit RSA keys. Signatures can have the RSA 1.5 or PSS format.
- To create a new key pair, select the type of key to generate from the bottom of the screen (using SSH-2 RSA with 2048 bit key size is good for most people; another good well-known alternative is ECDSA). Then click Generate, and start moving the mouse within the Window. Putty uses mouse movements to.
- In Table 2 of that document, it says 2048-bit RSA keys are roughly equivalent to a Security Strength of 112. Security strength is simply a number associated with the amount of work required to break a cryptographic algorithm. Basically, the higher that number, the greater the amount of work required.
by
Looking for ZRTP, TLS and 4096 bit RSA in a 100% free and open-source Android app? Lumicall
Many people are taking a fresh look at IT security strategies in the wake of the NSA revelations. One of the issues that comes up is the need for stronger encryption, using public key cryptography instead of just passwords. This is sometimes referred to as certificate authentication, but certificates are just one of many ways to use public key technology.
One of the core decisions in this field is the key size. Most people have heard that 1024 bit RSA keys have been cracked and are not used any more for web sites or PGP. The next most fashionable number after 1024 appears to be 2048, but a lot of people have also been skipping that and moving to 4096 bit keys. This has lead to some confusion as people try to make decisions about which smartcards to use or which type of CA certificate to use. The discussion here is exclusively about RSA key pairs, although the concepts are similar for other algorithms (although key lengths are not equivalent)
Instead of disclosing the key, the access point (AP) and client encrypt messages to each other—that can only be decrypted by using the PMK that they already share—and if decryption of the messages was successful, this proves knowledge of the PMK. If an 802.1X EAP exchange was carried out, the PMK is derived from the EAP parameters provided by the authentication server.Four-way handshakeThe four-way handshake is designed so that the access point (or authenticator) and wireless client (or supplicant) can independently prove to each other that they know the PSK/PMK, without ever disclosing the key. In PSK authentication, the PMK is actually the PSK, which is typically derived from WiFi password by putting it through a that use as the. This process ensures that the client station (STA) is authenticated with the access point (AP). After the PSK or 802.1X authentication, a shared secret key is generated, called the (PMK). In 802.11i pre-shared key mode the initial key is generated movie.
The case for using 2048 bits instead of 4096 bits
- Some hardware (many smart cards, some card readers, and some other devices such as Polycom phones) don't support anything bigger than 2048 bits.
- Uses less CPU than a longer key during encryption and authentication
- Using less CPU means using less battery drain (important for mobile devices)
- Uses less storage space: while not an issue on disk, this can be an issue in small devices like smart cards that measure their RAM in kilobytes rather than gigabytes
So in certain situations, there are some clear benefits of using 2048 bit keys and not just jumping on the 4096 bit key bandwagon
The case for using 4096 bits
- If an attack is found that allows a 2048 bit key to be hacked in 100 hours, that does not imply that a 4096 bit key can be hacked in 200 hours. The hack that breaks a 2048 bit key in 100 hours may still need many years to crack a single 4096 bit key. It is also worth noting that simply adding 1 bit (going from 1024 bits to 1025 bits) does not double the effort to crack the key, each extra bit adds some security but a little bit less than what was gained with the previous bit. There is a law of diminishing returns with RSA key length.
- Some types of key (e.g. an OpenPGP primary key which is signed by many other people) are desirable to keep for an extended period of time, perhaps 10 years or more. In this context, the hassle of replacing all those signatures may be quite high and it is more desirable to have a long-term future-proof key length.
The myth of certificate expiration
Many types of public key cryptography, such as X.509, offer an expiry feature. This is not just a scheme to force you to go back to the certificate authority and pay more money every 12 months. It provides a kind of weak safety net in the case where somebody is secretly using an unauthorised copy of the key or a certificate that the CA issued to an imposter.
However, the expiry doesn't eliminate future algorithmic compromises. If, in the future, an attacker succeeds in finding a shortcut to break 2048 bit keys, then they would presumably crack the root certificate as easily as they crack the server certificates and then, using their shiny new root key, they would be in a position to issue new server certificates with extended expiry dates.
Therefore, the expiry feature alone doesn't protect against abuse of the key in the distant future. It does provide some value though: forcing people to renew certificates periodically allows the industry to bring in new minimum key length standards from time to time.
In practical terms, content signed with a 2048 bit key today will not be valid indefinitely. Imagine in the year 2040 you want to try out a copy of some code you released with a digital signature in 2013. In 2040, that signature may not be trustworthy: most software in that era would probably see the key and tell you there is no way you can trust it. The NIST speculates that 2048 bit keys will be valid up to about the year 2030, so that implies that any code you sign with a 2048 bit key today will have to be re-signed with a longer key in the year 2029. You would do that re-signing in the 2048 bit twilight period while you still trust the old signature.
4096 in practice
One of the reasons I decided to write this blog is the fact that some organisations have made the 4096 bit keys very prominent (although nobody has made them mandatory as far as I am aware).
Debian's guide to key creation currently recommends 4096 bit keys (although it doesn't explicitly mandate their use)
Fedora's archive keys are all 4096 bit keys.
The CACert.org project has developed a 4096 bit root
These developments may leave people feeling a little bit naked if they have to use a shorter 2048 bit key for any of the reasons suggested above (e.g. for wider choice of smart cards and compatibility with readers). It has also resulted in some people spending time looking for 4096 bit smart cards and compatible readers when they may be better off just using 2048 bits and investing their time in other security improvements.
In fact, the 'risk' of using only 2048 rather than 4096 bits in the smartcard may well be far outweighed by the benefits of hardware security (especially if a < a href='https://www.opensc-project.org/opensc/wiki/PinpadReaders'>smartcard reader with pin-pad is used)
My own conclusion is that 2048 is not a dead duck and using this key length remains a valid decision and is very likely to remain so for the next 5 years at least. The US NIST makes a similar recommendation and suggests it will be safe until 2030, although it is the minimum key length they have recommended.
My feeling is that the Debian preference for 4096 bit PGP keys is not based solely on security, rather, it is also influenced by the fact that Debian is a project run by volunteers. Given this background, there is a perception that if everybody migrates from 1024 to 2048, then there would be another big migration effort to move all users from 2048 to 4096 and that those two migrations could be combined into a single effort going directly from 1024 to 4096, reducing the future workload of the volunteers who maintain the keyrings. This is a completely rational decision for administrative reasons, but it is not a decision that questions the security of using 2048 bit keys today. Therefore, people should not see Debian's preference to use 4096 bit keys as a hint that 2048 bit keys are fundamentally flawed.
Unlike the Debian keys (which are user keys), the CACert.org roots and Fedora archive signing keys are centrally managed keys with a long lifetime and none of the benefits of using 2048 bit keys is a compelling factor in those use cases.
Practical issues to consider when choosing key-length
Therefore, the choice of using 2048 or 4096 is not pre-determined, and it can be balanced with a range of other decisions:
- Key lifetime: is it a long life key, such as an X.509 root for an in-house CA or an OpenPGP primary key? Or is it just for a HTTPS web server or some other TLS server that can be replaced every two years?
- Is it for a dedicated application (e.g. a closed user group all using the same software supporting 4096 bit) or is it for a widespread user base where some users need to use 2048 bit due to old software/hardware?
- Is it necessary to use the key(s) in a wide variety of smartcard readers?
- Is it a mobile application (where battery must be conserved) or a server that is likely to experience heavy load?
Looking for ZRTP, TLS and 4096 bit RSA in a1 100% free and open-source Android app? Lumicall
tags: promoteTheoretically, RSA keys that are 2048 bits long should be good until 2030. If so, isn't it a bit early to start using the 4096-bit keys that have become increasingly available in encryption-enabled applications? It depends.
In case you're curious where we got the idea of 2048-bit keys being safe to use until 2030, check out the NIST Special Publication 800-57 Part1. In Table 2 of that document, it says 2048-bit RSA keys are roughly equivalent to a Security Strength of 112. Security strength is simply a number associated with the amount of work required to break a cryptographic algorithm. Basically, the higher that number, the greater the amount of work required.
We have reproduced a portion of that table below for those who want a quick reference. It implies longer keys are more difficult to break and are hence more secure.
| Security Strength | RSA key length |
| <= 80 | 1024 |
| 112 | 2048 |
| 128 | 3072 |
| 192 | 7680 |
| 256 | 15360 |
The same NIST document also has a table (Table 4) that shows the period over which each Security Strength is deemed acceptable. According to that publication, 112 security strength (which corresponds to 2048-bit keys) is considered to be acceptable until 2030. Again, here's a portion of that table for reference.
| Security Strength | Through 2030 | 2031 and beyond |
| < 112 | Disallowed | Disallowed |
| 112 | Acceptabe | Disallowed |
| 128 | Acceptable | Acceptable |
| 192 | Acceptable | Acceptable |
| 256 | Acceptable | Acceptable |
Alright. So now we know 2048 bit keys are indeed acceptable until 2030 as per NIST. So where does that put our 4096 bit keys? Incidentally, the document is silent about this particular key length. However, because the two tables indicate that 3072-bit keys (whose security strength is 128) and 7680-bit keys (whose security strength is 192) are good beyond 2030, we can safely say 4096 bit keys (which are somewhere in between) should likewise be considered secure enough then.
In fact, since 2048-bit keys are supposed to be disallowed after 2030, we know for certain that 4096 bit keys are going to be more suitable in production environments than 2048 keys when that time comes. But since we're still at least a decade away from 2030, it's probably not yet necessary to migrate from 2048 to 4096, right?
So why then are we already seeing options for 4096-bit keys in some security applications?
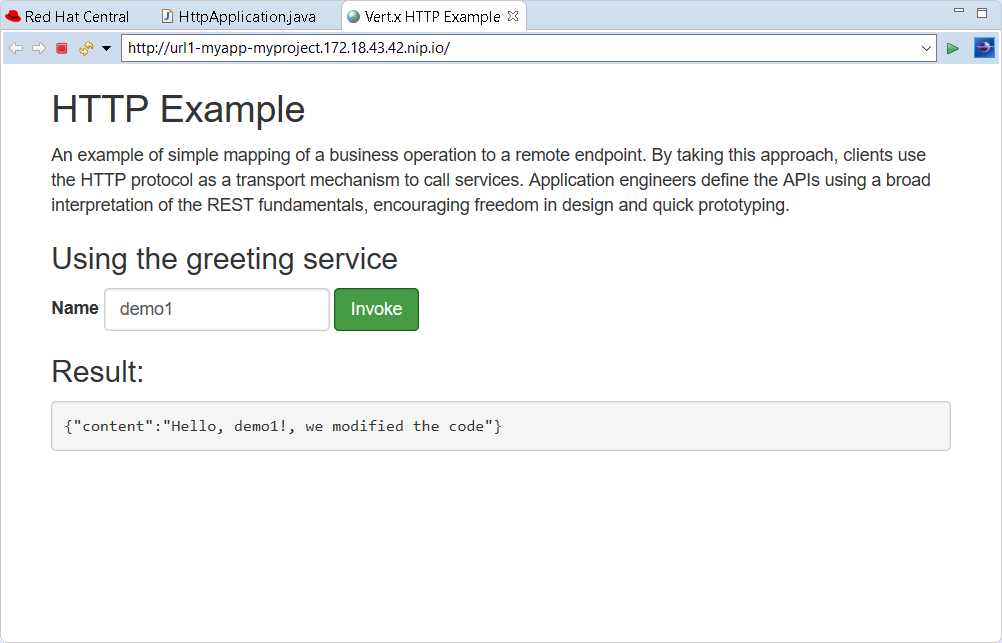
4096-bit key provided as an option during server key generation on JSCAPE MFT Server v10.2
Crack 2048 Bit Rsa Key
Well, there could be a couple of reasons. One is simply to make the application future proof. A future proof security solution can mitigate the risk of cyber threats. We know that cyber criminals are always one step ahead of security professionals, so we're not 100% sure 2048-bit keys are going to remain unbreakable before 2030.
But if the more secure 4096 keys are already available and it's just a matter of clicking the 4096 option, what should stop us from doing just that? One factor that needs to be considered is performance. Longer keys take more time to generate and require more CPU and power when used for encrypting and decrypting. So, in the case of file transfer servers, if your physical server is relatively old and has limited computing resources, then 4096-bit keys may impact your server's performance.
Actually, secure file transfer protocols like HTTPS, FTPS, or SFTP normally use RSA keys only during the start of the connection, when they're used in encrypting the symmetric keys. Once you start transmitting the data, it's going to be the symmetric keys that are going to be used in the subsequent encryption processes.
So, the performance hit due to a 4096-bit key will only be felt within a small fraction of the entire file transfer session. Of course, if your server carries out a large number of concurrent file transfers, then the performance hits can add up. But just how significant are these performance hits? That would depend on several factors like your server's CPU, the number of concurrent file transfers, network bandwidth, and so on.
In other words, the impact on performance would vary from one scenario to another. The best way to determine if the performance hit would be substantial in your particular environment would be to run actual tests.
2048-bit Rsa Key Generator
JSCAPE MFT Server v10.2, which is due for release on December 8, 2017, already supports 4096-bit keys. So if you want to run some tests against it to see if the performance hits are substantial in your specific environment, then you may download an evaluation edition as soon as it's available. We shall update this blog post with a download link once version 10.2 is out.
Dsa Key
You can run performance tests against that JSCAPE MFT Server instance using the load testing feature of JSCAPE MFT Monitor. We've written a blog post featuring a rudimentary load testing session involving key lengths some time in the past. To get some ideas from there, read the post:
Choosing Key Lengths for Encrypted File Transfers
Rsa 2048 Bits
Other related posts
Setting Up An SFTP Server