Ssl Key Generate With Password
Jul 09, 2019 Can I generate a new Private Key for my Certificate if I lose the old one? You can generate a new private key and CSR, or use the automatic CSR and key generation during Certificate reissue (this option is available for all Certificates except for the Multi-Domains). What does the Private Key look like? Free SSL Certificate issued in less than a minute. 100% Free Forever. Never pay for SSL again. Thanks to Letsencrypt the first non-profit CA. Widely Trusted. Our free SSL certificates are trusted in 99.9% of all major browsers.
Note: take into account that my final goal is to generate a p12 file by combining the certificate provided according to the CSR and the private key (secured with a password). Jul 09, 2019 WHM stores your private keys and CSR codes in the SSL Storage Manager menu. On the homepage, click SSL/TLS SSL Storage Manager. To view the Private Key, click the magnifier icon next to the relevant key in the Key column. Click Domains your domain SSL/TLS Certificates. You’ll see a page like the one shown below.
While Encrypting a File with a Password from the Command Line using OpenSSLis very useful in its own right, the real power of the OpenSSL library is itsability to support the use of public key cryptograph for encrypting orvalidating data in an unattended manner (where the password is not required toencrypt) is done with public keys.
The Commands to Run
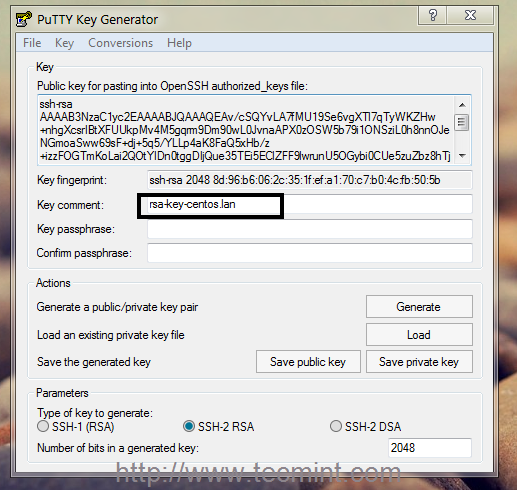
Generate a 2048 bit RSA Key
You can generate a public and private RSA key pair like this:
openssl genrsa -des3 -out private.pem 2048
That generates a 2048-bit RSA key pair, encrypts them with a password you provideand writes them to a file. You need to next extract the public key file. You willuse this, for instance, on your web server to encrypt content so that it canonly be read with the private key.
Export the RSA Public Key to a File
This is a command that is
openssl rsa -in private.pem -outform PEM -pubout -out public.pem
The -pubout flag is really important. Be sure to include it.
Next open the public.pem and ensure that it starts with-----BEGIN PUBLIC KEY-----. This is how you know that this file is thepublic key of the pair and not a private key.
To check the file from the command line you can use the less command, like this:
less public.pem
Do Not Run This, it Exports the Private Key
A previous version of the post gave this example in error.
openssl rsa -in private.pem -out private_unencrypted.pem -outform PEM
The error is that the -pubout was dropped from the end of the command.That changes the meaning of the command from that of exporting the public keyto exporting the private key outside of its encrypted wrapper. Inspecting theoutput file, in this case private_unencrypted.pem clearly shows that the keyis a RSA private key as it starts with -----BEGIN RSA PRIVATE KEY-----.
Visually Inspect Your Key Files
It is important to visually inspect you private and public key files to makesure that they are what you expect. OpenSSL will clearly explain the nature ofthe key block with a -----BEGIN RSA PRIVATE KEY----- or -----BEGIN PUBLIC KEY-----.
You can use less to inspect each of your two files in turn:
less private.pemto verify that it starts with a-----BEGIN RSA PRIVATE KEY-----less public.pemto verify that it starts with a-----BEGIN PUBLIC KEY-----
The next section shows a full example of what each key file should look like.
The Generated Key Files
The generated files are base64-encoded encryption keys in plain text format.If you select a password for your private key, its file will be encrypted withyour password. Be sure to remember this password or the key pair becomes useless.
The private.pem file looks something like this:
The public key, public.pem, file looks like:
Protecting Your Keys
Depending on the nature of the information you will protect, it’s important tokeep the private key backed up and secret. The public key can be distributedanywhere or embedded in your web application scripts, such as in your PHP,Ruby, or other scripts. Again, backup your keys!
Remember, if the key goes away the data encrypted to it is gone. Keeping aprinted copy of the key material in a sealed envelope in a bank safety depositbox is a good way to protect important keys against loss due to fire or harddrive failure.
Oh, and one last thing.
If you, dear reader, were planning any funny business with the private key that I have just published here. Know that they were made especially for this series of blog posts. I do not use them for anything else.
Found an issue?
Rietta plans, develops, and maintains applications.
Learn more about our services or drop us your email and we'll e-mail you back.
Other Blog Articles Published by Rietta.com
Use Java's Keytool to create a CSR and install your SSL/TLS certificate on your Tomcat (or other Java-based) server
Use these instructions to generate your certificate signing request (CSR) and install your SSL/TLS certificate on your Tomcat server using Java’s Keytool.
Restart Note: After you've installed your SSL/TLS certificate and configured the server to use it, you must restart the Tomcat service.
To create your certificate signing request (CSR), see Tomcat Server: Create Your CSR with Java Keytool.
To install your SSL certificate, see Tomcat Server: Install and Configure Your SSL/TLS Certificate.
To view these instructions in Spanish, see CSR para Tomcat and Tomcat Instalar Certificado SSL.
If you are looking for a simpler way to create CSRs, and install and manage your SSL/TLS certificates, we recommend using the DigiCert® Certificate Utility for Windows. You can use the DigiCert Utility to generate your CSR and prepare your SSL/TLS certificate file for installation on your Tomcat server. See Tomcat: Create CSR & Install SSL/TLS Certificate with the DigiCert Utility.
I. Tomcat Server: Create Your CSR with Java’s Keytool
Use the instructions in this section to create a new keystore (.jks) file and to generate your CSR.
Recommended Method: Use the DigiCert Java Keytool CSR Wizard
Save yourself some time: Use the DigiCert Java Keytool CSR Wizard to generate a Keytool command to create your Tomcat keystore and CSR.
Simply fill out the form, click Generate, and then paste your customized Java Keytool command into your terminal.
The Java keytool utility creates both your private key and your certificate signing request, and saves them to two files: your_common_name.jks, and your_common_name.csr.
You can then copy the contents of the CSR file and paste it into the CSR text box in our order form.
Skip to Step 2, part 3: Save and Back-up Your Keystore File.
Do you prefer a more manual approach to generating your Tomcat keystore and CSR? Follow the instructions below.
Step 1: Use Keytool to Create a New Keystore
Ssl Key Generate With Password Key
Important: We recommend you generate a new keystore following the process outlined in this section. Installing a new certificate to an old keystore often ends in installation errors or the SSL/TLS certificate not working properly. Before you begin this process, backup and remove any old keystores.
Run Command
Navigate to the directory where you plan to manage your keystore and SSL/TLS certificate.
Enter the command below.
In the command above, your_site_name should be the name of the domain you want to secure with this SSL/TLS certificate. When ordering a Wildcard certificate, do not include the asterisk (*) in the filename (e.g., your_site_name). The asterisk is not a valid keytool character.
Create a Password
When prompted, create a password for your Keystore.
Note: You will specify this password in your Tomcat configuration file and then use it to generate your CSR and to import your certificate.
Store this password somewhere safe, such as a trusted and secured password manager.
Enter your SSL/TLS certificate information.
Important: When prompted for the first and last name, DO NOT type your first and last name. Instead, type the Fully Qualified Domain Name (FQDN) for the site you are securing with this certificate (e.g., www.yourdomain.com, mail.yourdomain.com). Are you are ordering a Wildcard Certificate? Then your FQDN must begin with an asterisk (*). (e.g.,*.yourdomain.com).
Enter your Organization information.
When prompted to verify your information, type y or yes to confirm.
When asked for a 'key password for <server>', press enter to use the password you just created for the keystore file.
Your keystore file, your_site_name.jks, is now created and in your current working directory.
Ssl Key Generate With Password Code
Step 2: Generate a Certificate Signing Request (CSR) from your New Keystore
Key Generator Download
Run Command
In Keytool, type the following command:
Star wars battlefront season pass key generator. Enter the Code. Paste or type in the code you found into the coupon box and submit it. Some merchants let you stack coupons and promo codes. Then, you will see your discount applied to your balance.
In the command above, your_site_name should be the name of the keystore file you created in Step 1: Use Keytool to Create a New Keystore or when using the DigiCert Java Keytool CSR Wizard.
When prompted, enter the password you created earlier (when you created your new keystore).
Cs go steam key generator online free. About This GameCounter-Strike: Global Offensive (CS: GO) expands upon the team-based action gameplay that it pioneered when it was launched 19 years ago.CS: GO features new maps, characters, weapons, and game modes, and delivers updated versions of the classic CS content (dedust2, etc.).' 'For the past 12 years, it has continued to be one of the most-played games in the world, headline competitive gaming tournaments and selling over 25 million units worldwide across the franchise. Counter-Strike took the gaming industry by surprise when the unlikely MOD became the most played online PC action game in the world almost immediately after its release in August 1999,' said Doug Lombardi at Valve. CS: GO promises to expand on CS' award-winning gameplay and deliver it to gamers on the PC as well as the next gen consoles and the Mac.'
In your current directory, csr.txt (e.g., your_site_domain.txt) now contains your CSR.
Save and Back-up Your Keystore File
Take note of the path to your keystore file (your_site_domain.jks) as your SSL/TLS certificate will be installed to it later.
We recommend that you create a back-up copy of your Keystore file (your_site_domain.jks) before continuing. Having a back-up of the Keystore file can help resolve issues that may occur during certificate SSL/TLS installation.
Order Your SSL/TLS Certificate
Open the .csr file you created with a text editor.
Copy the text, including the -----BEGIN NEW CERTIFICATE REQUEST----- and -----END NEW CERTIFICATE REQUEST----- tags, and paste it in to the DigiCert order form.
Make sure that when you Select Server Software, you select Tomcat.
Tomcat SSL/TLS Certificates, Guides, & Tutorials
Buy NowLearn MoreInstall Certificate
After you’ve received your SSL/TLS certificate from DigiCert, you can install it on your Tomcat server.