Elliptic Curve Key Generation Algorithm
- Elliptic Curve Key Generation Algorithm Download
- Create Elliptic Curve Key
- Elliptic Curve Cryptography Key Generation
- Elliptic Curve Key Generation Algorithm In Cryptography
Elliptic Curve Key Generation Algorithm Download
Jan 10, 2019 ECDSA (Elliptic Curve Digital Signature Algorithm) is based on DSA, but uses yet another mathematical approach to key generation. ECC is a mathematical equation taken on its own, but ECDSA is the algorithm that is applied to ECC to make it appropriate for security encryption. Performance Comparison of Elliptic Curve and RSA Digital Signatures by Nicholas Jansma and Brandon Arrendondo. RSA key generation is significantly slower than ECC key generation for RSA key of sizes 1024 bits and greater. The cost of key generation can be considered as a factor in the choice of public key systems to use when using. Provides a Cryptography Next Generation (CNG) implementation of the Elliptic Curve Diffie-Hellman (ECDH) algorithm. The following example shows how to use the ECDiffieHellmanCng class to establish a key exchange and how to use that key to encrypt a message that can be sent over a. Gets or sets the hash algorithm to use when generating. With the support of configurable Key Pair generation, Elliptic named curves keys and operations (e.g X25519, X448.), Chinese Algorithms (SM2, SM3, SM4) and two additional AES modes (CFB, XTS) the Java Card 3.1 release brings major enhancements to meet the security requirements of both existing secure chips and emerging IoT technologies. Creates a new instance of the default implementation of the Elliptic Curve Digital Signature Algorithm (ECDSA). Creates a new instance of the default implementation of the Elliptic Curve Digital Signature Algorithm (ECDSA) with a newly generated key over the specified curve.
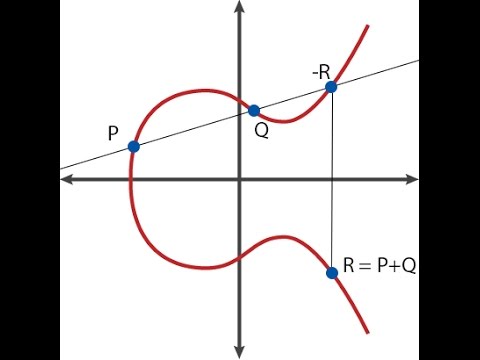
Oct 24, 2013 CloudFlare uses elliptic curve cryptography to provide perfect forward secrecy which is essential for online privacy. First generation cryptographic algorithms like RSA and Diffie-Hellman are still the norm in most arenas, but elliptic curve cryptography is quickly becoming the go-to solution for privacy and security online. So far I've implemented the key generation algorithm, the point addition, doubling, encryption and decryption. Now my problem is the key generation. The formula for generating a key is: Q = d. G. Where Q is the public key, d is the private key and G the generator point.
Definition
Provides a Cryptography Next Generation (CNG) implementation of the Elliptic Curve Diffie-Hellman (ECDH) algorithm. This class is used to perform cryptographic operations.
Examples
The following example shows how to use the ECDiffieHellmanCng class to establish a key exchange and how to use that key to encrypt a message that can be sent over a public channel and decrypted by the receiver.
Remarks
The ECDiffieHellmanCng class enables two parties to exchange private key material even if they are communicating through a public channel. Both parties can calculate the same secret value, which is referred to as the secret agreement in the managed Diffie-Hellman classes. The secret agreement can then be used for a variety of purposes, including as a symmetric key. However, instead of exposing the secret agreement directly, the ECDiffieHellmanCng class does some post-processing on the agreement before providing the value. This post processing is referred to as the key derivation function (KDF); you can select which KDF you want to use and set its parameters through a set of properties on the instance of the Diffie-Hellman object.
| Key derivation function | Properties |
|---|---|
| Hash | HashAlgorithm - The hash algorithm that is used to process the secret agreement. SecretPrepend - An optional byte array to prepend to the secret agreement before hashing it. SecretAppend - An optional byte array to append to the secret agreement before hashing it. |
| Hmac | HashAlgorithm - The hash algorithm that is used to process the secret agreement. SecretPrepend- An optional byte array to prepend to the secret agreement before hashing it. SecretAppend - An optional byte array to append to the secret agreement before hashing it. |
| Tls | Label - The label for key derivation. Seed - The seed for key derivation. |
The result of passing the secret agreement through the key derivation function is a byte array that may be used as key material for your application. The number of bytes of key material generated is dependent on the key derivation function; for example, SHA-256 will generate 256 bits of key material, whereas SHA-512 will generate 512 bits of key material.The basic flow of an ECDH key exchange is as follows:
Alice and Bob create a key pair to use for the Diffie-Hellman key exchange operation
Alice and Bob configure the KDF using parameters the agree on.
Alice sends Bob her public key.
Bob sends Alice his public key.
Alice and Bob use each other's public keys to generate the secret agreement, and apply the KDF to the secret agreement to generate key material.
Constructors
| ECDiffieHellmanCng() | Initializes a new instance of the ECDiffieHellmanCng class with a random key pair. |
| ECDiffieHellmanCng(CngKey) | Initializes a new instance of the ECDiffieHellmanCng class by using the specified CngKey object. |
| ECDiffieHellmanCng(ECCurve) | Creates a new instance of the ECDiffieHellmanCng class whose public/private key pair is generated over the specified curve. |
| ECDiffieHellmanCng(Int32) | Initializes a new instance of the ECDiffieHellmanCng class with a random key pair, using the specified key size. |
Fields
| KeySizeValue | Represents the size, in bits, of the key modulus used by the asymmetric algorithm. (Inherited from AsymmetricAlgorithm) |
| LegalKeySizesValue | Specifies the key sizes that are supported by the asymmetric algorithm. (Inherited from AsymmetricAlgorithm) |
Properties
Create Elliptic Curve Key
| HashAlgorithm | Gets or sets the hash algorithm to use when generating key material. |
| HmacKey | Gets or sets the Hash-based Message Authentication Code (HMAC) key to use when deriving key material. |
| Key | Specifies the CngKey that is used by the current object for cryptographic operations. |
| KeyDerivationFunction | Gets or sets the key derivation function for the ECDiffieHellmanCng class. |
| KeyExchangeAlgorithm | Gets the name of the key exchange algorithm. (Inherited from ECDiffieHellman) |
| KeySize | Gets or sets the size, in bits, of the key modulus used by the asymmetric algorithm. |
| Label | Gets or sets the label value that is used for key derivation. |
| LegalKeySizes | Gets the key sizes that are supported by the asymmetric algorithm. (Inherited from AsymmetricAlgorithm) |
| PublicKey | Gets the public key that can be used by another ECDiffieHellmanCng object to generate a shared secret agreement. |
| SecretAppend | Gets or sets a value that will be appended to the secret agreement when generating key material. |
| SecretPrepend | Gets or sets a value that will be added to the beginning of the secret agreement when deriving key material. |
| Seed | Gets or sets the seed value that will be used when deriving key material. |
| SignatureAlgorithm | Gets the name of the signature algorithm. (Inherited from ECDiffieHellman) |
| UseSecretAgreementAsHmacKey | Gets a value that indicates whether the secret agreement is used as a Hash-based Message Authentication Code (HMAC) key to derive key material. |
Elliptic Curve Cryptography Key Generation
Methods
| Clear() | Releases all resources used by the AsymmetricAlgorithm class. (Inherited from AsymmetricAlgorithm) |
| DeriveKeyFromHash(ECDiffieHellmanPublicKey, HashAlgorithmName) | Performs key derivation using a specified hash algorithm. (Inherited from ECDiffieHellman) |
| DeriveKeyFromHash(ECDiffieHellmanPublicKey, HashAlgorithmName, Byte[], Byte[]) | Performs key derivation using a specified hash algorithm with optional prepended or appended data. |
| DeriveKeyFromHmac(ECDiffieHellmanPublicKey, HashAlgorithmName, Byte[]) | Performs key derivation using a specified HMAC (Hash-based Message Authentication Code) algorithm. (Inherited from ECDiffieHellman) |
| DeriveKeyFromHmac(ECDiffieHellmanPublicKey, HashAlgorithmName, Byte[], Byte[], Byte[]) | Performs key derivation using a specified HMAC (Hash-based Message Authentication Code) algorithm with optional prepended or appended data. |
| DeriveKeyMaterial(CngKey) | Derives the key material that is generated from the secret agreement between two parties, given a CngKey object that contains the second party's public key. |
| DeriveKeyMaterial(ECDiffieHellmanPublicKey) | Derives the key material that is generated from the secret agreement between two parties, given an ECDiffieHellmanPublicKey object that contains the second party's public key. |
| DeriveKeyTls(ECDiffieHellmanPublicKey, Byte[], Byte[]) | Performs key derivation using the TLS (Transport Layer Security) 1.1 PRF (Pseudo-Random Function). |
| DeriveSecretAgreementHandle(CngKey) | Gets a handle to the secret agreement generated between two parties, given a CngKey object that contains the second party's public key. |
| DeriveSecretAgreementHandle(ECDiffieHellmanPublicKey) | Gets a handle to the secret agreement generated between two parties, given an ECDiffieHellmanPublicKey object that contains the second party's public key. |
| Dispose() | Releases all resources used by the current instance of the AsymmetricAlgorithm class. (Inherited from AsymmetricAlgorithm) |
| Dispose(Boolean) | Releases the unmanaged resources used by the AsymmetricAlgorithm class and optionally releases the managed resources. (Inherited from AsymmetricAlgorithm) |
| Equals(Object) | Determines whether the specified object is equal to the current object. (Inherited from Object) |
| ExportECPrivateKey() | Exports the current key in the ECPrivateKey format. (Inherited from ECDiffieHellman) |
| ExportEncryptedPkcs8PrivateKey(ReadOnlySpan<Byte>, PbeParameters) | Exports the current key in the PKCS#8 EncryptedPrivateKeyInfo format with a byte-based password. (Inherited from AsymmetricAlgorithm) |
| ExportEncryptedPkcs8PrivateKey(ReadOnlySpan<Char>, PbeParameters) | Exports the current key in the PKCS#8 EncryptedPrivateKeyInfo format with a char-based password. (Inherited from AsymmetricAlgorithm) |
| ExportExplicitParameters(Boolean) | Exports the key and explicit curve parameters used by the ECCurve object into an ECParameters object. |
| ExportParameters(Boolean) | Exports the key used by the ECCurve object into an ECParameters object. |
| ExportPkcs8PrivateKey() | Exports the current key in the PKCS#8 PrivateKeyInfo format. (Inherited from AsymmetricAlgorithm) |
| ExportSubjectPublicKeyInfo() | Exports the public-key portion of the current key in the X.509 SubjectPublicKeyInfo format. (Inherited from AsymmetricAlgorithm) |
| FromXmlString(String) | This method is not implemented. |
| FromXmlString(String, ECKeyXmlFormat) | Deserializes the key information from an XML string by using the specified format. |
| GenerateKey(ECCurve) | Generates a new ephemeral public/private key pair for the specified curve. |
| GetHashCode() | Serves as the default hash function. (Inherited from Object) |
| GetType() | Gets the Type of the current instance. (Inherited from Object) |
| ImportECPrivateKey(ReadOnlySpan<Byte>, Int32) | Imports the public/private keypair from an ECPrivateKey structure, replacing the keys for this object. (Inherited from ECDiffieHellman) |
| ImportEncryptedPkcs8PrivateKey(ReadOnlySpan<Byte>, ReadOnlySpan<Byte>, Int32) | Imports the public/private keypair from a PKCS#8 EncryptedPrivateKeyInfo structure after decrypting with a byte-based password, replacing the keys for this object. (Inherited from ECDiffieHellman) |
| ImportEncryptedPkcs8PrivateKey(ReadOnlySpan<Char>, ReadOnlySpan<Byte>, Int32) | Imports the public/private keypair from a PKCS#8 EncryptedPrivateKeyInfo structure after decrypting with a char-based password, replacing the keys for this object. (Inherited from ECDiffieHellman) |
| ImportParameters(ECParameters) | Imports the specified parameters for an ECCurve object as a key into the current instance. |
| ImportPkcs8PrivateKey(ReadOnlySpan<Byte>, Int32) | Imports the public/private keypair from a PKCS#8 PrivateKeyInfo structure after decryption, replacing the keys for this object. (Inherited from ECDiffieHellman) |
| ImportSubjectPublicKeyInfo(ReadOnlySpan<Byte>, Int32) | Imports the public key from an X.509 SubjectPublicKeyInfo structure after decryption, replacing the keys for this object. (Inherited from ECDiffieHellman) |
| MemberwiseClone() | Creates a shallow copy of the current Object. (Inherited from Object) |
| ToString() | Returns a string that represents the current object. (Inherited from Object) |
| ToXmlString(Boolean) | This method is not implemented. |
| ToXmlString(ECKeyXmlFormat) | Serializes the key information to an XML string by using the specified format. |
| TryExportECPrivateKey(Span<Byte>, Int32) | Attempts to export the current key in the ECPrivateKey format into a provided buffer. (Inherited from ECDiffieHellman) |
| TryExportEncryptedPkcs8PrivateKey(ReadOnlySpan<Byte>, PbeParameters, Span<Byte>, Int32) | Attempts to export the current key in the PKCS#8 EncryptedPrivateKeyInfo format into a provided buffer, using a byte-based password. (Inherited from ECDiffieHellman) |
| TryExportEncryptedPkcs8PrivateKey(ReadOnlySpan<Char>, PbeParameters, Span<Byte>, Int32) | Attempts to export the current key in the PKCS#8 EncryptedPrivateKeyInfo format into a provided buffer, using a char-based password. (Inherited from ECDiffieHellman) |
| TryExportPkcs8PrivateKey(Span<Byte>, Int32) | Attempts to export the current key in the PKCS#8 PrivateKeyInfo format into a provided buffer. About RandomKeygen. Our free mobile-friendly tool offers a variety of randomly generated keys and passwords you can use to secure any application, service or device. Simply click to copy a password or press the 'Generate' button for an entirely new set. Password Recommendations. Secret key indonesia. (Inherited from ECDiffieHellman) |
| TryExportSubjectPublicKeyInfo(Span<Byte>, Int32) | Attempts to export the current key in the X.509 SubjectPublicKeyInfo format into a provided buffer. (Inherited from ECDiffieHellman) |
Explicit Interface Implementations
| IDisposable.Dispose() | For a description of this member, see Dispose(). (Inherited from AsymmetricAlgorithm) |